6.1 KiB
Privacy scoring modelling > Web3privacy now analytical platform
MVP for non-techies expanded to techies
Sandbox: DeFi category that has been analyzed
How to use sandbox?
- Read scoring assumptions below.
- Give us feedback via Pull request here.
- You can always explore scoring MVP based on 38 DeFi project' assessment here
important note: here "techies" covers "juniors" & general "developers" (masses) & not aplicable to "lead", "seniors" or even "mid"-devs (core devs).
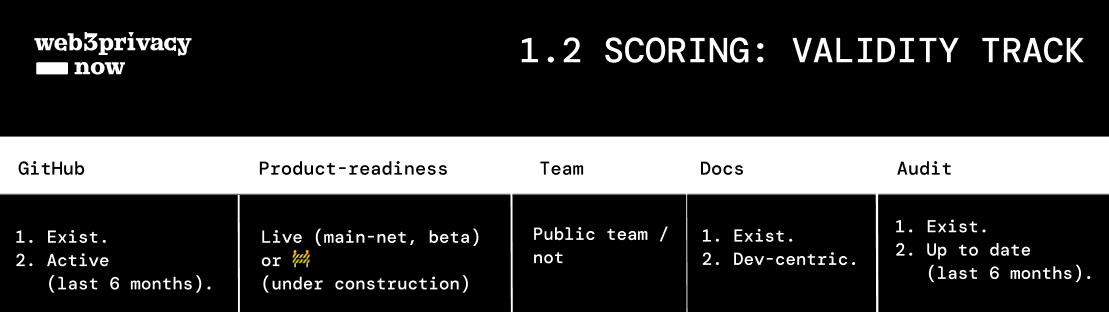
Scoring model 1.2: validity track
Validity track covers GitHub, Product-readiness, Team, Docs, Audit.
Note: quick assessment helps to decrease privacy dark patterns from obscure language to test-net claiming it has a "state of art privacy".
Sandbox
Extended scoring 1.0
| Project | GitHub | Product-readiness | Team | Docs | Audit | Contributors | Licenses | Support | Score |
|---|---|---|---|---|---|---|---|---|---|
| Test project | available & active GitHub / not (25%) | Live or 🚧 (exclusion criteria) | public team / not (25%) | available & not marketing docs / not (25%) | available & up to date third-party audit / not (25%) | external contributors outside of the team members | What licenses are in use | Some form of support available? (telegram, discord, forum) | from 0 to 100% |
| score | 12.5% | 12.5% | 12.5% | 12.5% | 12.5% | 12.5% | 12.5% | 12.5% | 100% |
Updates 1.1
GitHub
- Is it in stable release, 1.0 and not an alpha or untested code?
- Are there many PRs and Issues pending?
- Are there external contributors outside of the team members? Waku example
- What are licenses in use? Privy Apache-2.0 license
example: Free & Open Source Software is the foundation that enables you to check whatever you want. The hoprd client is released under GPLv3 license that allows you to do that (and also modify and re-distribute) Hoprn freely
Docs
- read the documentation: is it comprehensive?
- how well-written are privacy & security assumptions/guarantees?
- if aplicable: how well-written is encryption method? example
- is Whitepaper marketing or dev-centric?
Team
- Check if there are known contributors (reputation 101)
- Check commits at GitHub
- How many community contributors beyond core team?
- How many technical specialists in the team?
- How mature are core contributors (previous projects, GitHub commits)?
Third-party audit
- Were bugs fixed? Zokyo x Railgun_ example, p.7
- How centralized are product updates?
Infrastructure
| Scoring | Techie |
|---|---|
| Where are the nodes (check block explorer) Nym mainnet explorer | + |
| Number of nodes (the larger the footprint the best privacy) | + |
Data aggregation
| Scoring | Techie |
|---|---|
| no email or tel number for signup | + |
| does not implement KYC or AML | + |
| What user information is stored? (username, IP address, last connection, wallets associate, etc) | + |
Traction
| Scoring | Techie |
|---|---|
| Amount of transactions (Dune, DeFi Lama, block explorer etc) | + |
| number of people using it | + |
Governance
| Scoring | Techie |
|---|---|
| DAO structure (if applied) | + |
| How centralized is the protocol governance? Railgun_ governance docs | + |
Backlog
General
| Scoring | Techie |
|---|---|
| Immutability | + |
| Decentralised throughout, including hosting | + |
| Permissionless & accessible to all | + |
| Open-source | + |
Privacy policy
| Scoring | Techie |
|---|---|
| Privacy Policy content Railway zero data aggregation PP | + |
| Non-vague and non-intrusive privacy policy | + |
Storage
| Scoring | Techie |
|---|---|
| e2e encrypted LOCAL storage | + |
| Where is it stored? (centralized server, certain jurisdictions, on-chain, in browser/local cache) | + |
Privacy execution
| Scoring | Techie |
|---|---|
| p2p / no central server | + |
| Trustless - No ID required (this is where ZKs are useful) | + |
example: "with the unirep protocol we're building an explorer that shows all the things happening in the system. So a user could see their epoch keys and attestations and see how they're distinct in the system. One thing we might do is write what can and can't be determined about the different identifiers".
Testing
| Scoring | Techie |
|---|---|
| try to trace a transaction | + |
| Other tooling to verify e.g. block explorers | + |
Hardcore
from community
- use a packet inspection tool such as #Wireshark to check all packets coming into your machine and going out
- using something like https://charlesproxy.com to see all the traffic
- Android: Feel free to test it at @ExodusPrivacy, a friendly service to investigate Android apps.
- Android: check @fdroidorg and verify the “no anti-features” tag. We’ve worked hard to remove dependency on third-party services and strictly require user’s consent before opting-in to sharing information. Example